UNREDACTED Magazine
We are now preparing the next issue of UNREDACTED Magazine and we need more original articles (please do not send us links to something you already published). We are also seeking sponsors. If you have something to contribute, or wish to sponsor with a half-page or full-page ad, please contact us at [email protected].
Article Search
Use your browser's search feature to find specific articles.
| PAGE | ARTICLE | ISSUE |
| 2 | From The Editor | 001 |
| 3 | Email is Broken | 001 |
| 8 | An OSINT Backdoor to Utility Searches | 001 |
| 9 | I Installed Your Alarm System | 001 |
| 10 | Common Law Names and Cover ID | 001 |
| 13 | Successes and Failures of a Privacy Enthusiast | 001 |
| 16 | OSINT Corner | 001 |
| 17 | Intercepting Vehicle Maintenance Videos | 001 |
| 19 | New Google Content Removal Options | 001 |
| 20 | Leaving Kindle for BOOX | 001 |
| 22 | Reader Q&A | 001 |
| 24 | SD Card Backup Storage | 001 |
| 24 | Podcast Review | 001 |
| 25 | Sustainable Signals | 001 |
| 27 | Private USA Passport Renewal | 001 |
| 29 | Crossword | 001 |
| 30 | Final Thoughts | 001 |
| 5 | From the Editor | 002 |
| 6 | Maintaining Multiple Google Voice Numbers | 002 |
| 9 | Bypassing Privacy Invasions of State Parks | 002 |
| 10 | Anonymous in Tijuana | 002 |
| 12 | The Linux Lifestyle: Switching to Pop!_OS | 002 |
| 17 | How Did Amazon's Cameras ID Me? | 002 |
| 20 | When 2FA Harms More Than Helps | 002 |
| 21 | Choosing the Right Wireless Provider | 002 |
| 24 | The OSINT Corner | 002 |
| 26 | Eulogy for the iPod Touch | 002 |
| 27 | The Home Address Dilemma and Form I-9 | 002 |
| 28 | Fun With Radio Receivers | 002 |
| 30 | Reader Q&A | 002 |
| 33 | OSINT Book: Ubuntu Updates | 002 |
| 34 | Letters From Readers | 002 |
| 36 | Android Sanitization Package Names | 002 |
| 37 | My Secret Little Digital World | 002 |
| 39 | Wi-Fi Geolocation Concerns | 002 |
| 41 | Can Decentralized Identity Give You Greater Control? | 002 |
| 43 | Privacy-themed Puzzles | 002 |
| 44 | Final Thoughts | 002 |
| 5 | From the Editor | 003 |
| 6 | To PMB or Not to PMB: Private Mailboxes | 003 |
| 8 | Adding Kill Switches to Your Android Phone | 003 |
| 12 | The Linux Lifestyle: More Customization and Installation | 003 |
| 20 | Retrogaming and Privacy | 003 |
| 22 | Maintaining Multiple Signal Accounts | 003 |
| 24 | Purging Gmail Data Automatically | 003 |
| 26 | Exporting Authy 2FA Seed Codes | 003 |
| 28 | Using a De-Googled Pixel | 003 |
| 32 | The Radio Receiver: Monitoring Neighborhood Activity | 003 |
| 35 | Mitigating Risk of Online Service Failure | 003 |
| 38 | A Fresh Look at Standard Notes | 003 |
| 40 | The OSINT Corner Learning the Linux Command Line | 003 |
| 43 | HP Dev One with Pop!_OS | 003 |
| 46 | A FOSS Solution for Receiving Short Code SMS | 003 |
| 48 | Options for Your Domain | 003 |
| 51 | Apartment Living | 003 |
| 52 | Maintaining Privacy in the United Kingdom | 003 |
| 54 | The Case for Switching to Qubes OS | 003 |
| 57 | Reader Q&A | 003 |
| 59 | Book Updates | 003 |
| 60 | Letters | 003 |
| 63 | An Anonymous Cross-Country Road Trip | 003 |
| 65 | Privacy-themed Puzzles | 003 |
| 66 | Chuckles | 003 |
| 67 | Final Thoughts | 003 |
| 67 | Affiliate links | 003 |
| 5 | From the Editor | 004 |
| 6 | The Linux Lifestyle: USB Multi-Boot Options | 004 |
| 9 | Random Mosaic: Detecting Access with Beans & Rice | 004 |
| 12 | The Radio Receiver: Software Defined Radios | 004 |
| 17 | Bitcoin Privacy Tools & Tactics | 004 |
| 19 | Tracking Bitcoin: Tools for OSINT | 004 |
| 22 | My Digital Detox | 004 |
| 25 | The OSINT Corner Learning the Linux Command Line | 004 |
| 29 | Mobile OSINT Mastery: Utilizing iOS Shortcuts | 004 |
| 32 | Archive Site Removal Guide | 004 |
| 36 | When Stuff Gets Stuck | 004 |
| 39 | How Do Blockchains Provide the Trust Foundation | 004 |
| 42 | Paranoid Seller's Guide to Secondhand Marketplaces | 004 |
| 44 | How (not) to Fly Anonymously | 004 |
| 46 | More Android Sanitization | 004 |
| 48 | Using a Travel Router for Privacy on Public Wi-Fi | 004 |
| 49 | Is Revolut a viable alternative? | 004 |
| 50 | Encryption in the Age of Quantum Computing | 004 |
| 52 | Reader Q&A | 004 |
| 55 | Updates | 004 |
| 56 | Letters | 004 |
| 58 | Privacy-themed Puzzles | 004 |
| 59 | Chuckles | 004 |
| 60 | Final Thoughts | 004 |
| 60 | Affiliate links | 004 |
| 5 | From the Editor | 005 |
| 6 | The macOS Ventura Privacy & Security Guide | 005 |
| 12 | Wireless Security: Vehicle Remote Entry Attack and Defense | 005 |
| 15 | Malware or Mal-Awareness? | 005 |
| 19 | Social Links: Revolutionary AI-Driven OSINT solutions | 005 |
| 20 | An OSINT Practitioner’s Perspective on Privacy | 005 |
| 23 | Hardening Measures for Multi- Factor Authentications | 005 |
| 25 | Google Analytics | 005 |
| 28 | The OSINT Corner | 005 |
| 32 | Pet Intelligence | 005 |
| 34 | 10 Minutes of Google Dorking for COVID Documents | 005 |
| 37 | Supermarket Loyalty Card Privacy Strategy | 005 |
| 38 | Changing Your IMEI for Cellular Anonymity | 005 |
| 40 | Sign out of Apple | 005 |
| 42 | Reader Q&A | 005 |
| 44 | Updates | 005 |
| 45 | Letters | 005 |
| 46 | Verifiable Credentials: Decentralized Identity | 005 |
| 49 | Privacy-themed Puzzles | 005 |
| 50 | Final Thoughts | 005 |
| 50 | Affiliate links | 005 |
| 5 | From the Editor | 006 |
| 6 | Healthcare Privacy Considerations | 006 |
| 9 | Using Roku Players Privately | 006 |
| 12 | Address Confidentiality Programs | 006 |
| 18 | The Home Address Dilemma and Driver’s Licenses | 006 |
| 20 | Product Review SLNT E3 Faraday Backpack | 006 |
| 23 | Wireless Security | 006 |
| 29 | How your Apple account can be compromised | 006 |
| 32 | Getting Ready For A Post-Quantum World | 006 |
| 34 | Breaking Up With My Cell Phone Number of 21 Years | 006 |
| 37 | Cat and Mouse Part I: The Attack Framework | 006 |
| 39 | The OSINT Corner | 006 |
| 42 | Hunting Apps for OSINT | 006 |
| 44 | Elastichunt | 006 |
| 46 | Cutting Down on Browser Extensions | 006 |
| 49 | OSINT Exploring With MealTrain | 006 |
| 51 | The Secret Privacy Benefit of a Costco Card | 006 |
| 52 | Polyglot Passwords | 006 |
| 54 | Looking Beyond the Numbers | 006 |
| 56 | Offline Life: DAPs Revisited | 006 |
| 61 | Reader Q&A | 006 |
| 62 | Updates | 006 |
| 63 | Privacy-themed Puzzles | 006 |
| 64 | Final Thoughts | 006 |
| 64 | Affiliate links | 006 |
Digital Books
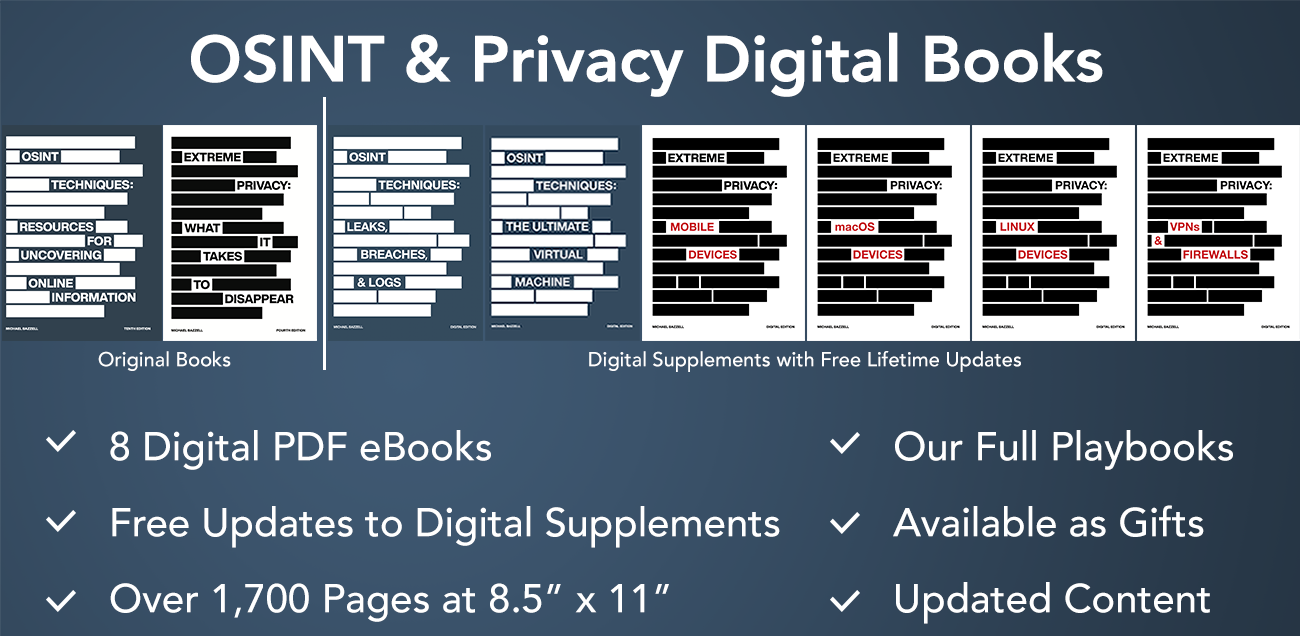
Buy Individual Books
Buy All 8 Books for $130
OSINT Techniques (10th Edition)
OSINT Techniques: Leaks, Breaches & Logs
OSINT Techniques: The Ultimate Virtual Machine
Extreme Privacy (4th Edition)
Extreme Privacy: Mobile Devices
Extreme Privacy: macOS Devices
Extreme Privacy: Linux Devices
Extreme Privacy: VPNs & Firewalls
Individual orders available on each book page. PDFs will be immediately available for download after purchase, and an email will also include the download link. You must provide an email address where we can reach you to deliver any updates. This can be a masked, forwarding, or private email provider, but please do not use temporary addresses which you will not be able to control in the future. All PDFs will include a visible and hidden watermark with your order number, but will not include your name, email, or any other personally identifying text. All orders are delivered via SendOwl, and purchasing details are submitted through our own Stripe account. We do not store your credit card information. Due to the nature of instant delivery of digital products, all sales are final.